Anatomy of a Penetration Test in UK
- May 14, 2026
- Posted by: Gradeon
- Category: Cyber Security
For many UK organisations, penetration testing is still seen as a final checkbox before compliance deadlines. That approach misses the real value.
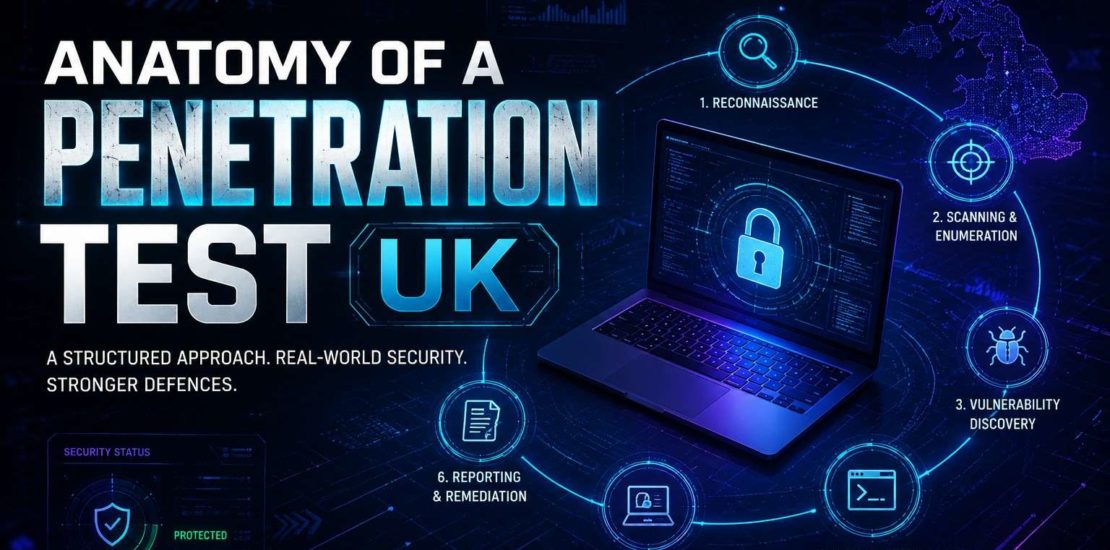
A professionally delivered penetration test is not just a vulnerability scan with a glossy PDF attached. It is a structured security assessment designed to simulate how a real attacker would identify weaknesses, exploit them, and demonstrate the potential business impact. The UK’s National Cyber Security Centre defines penetration testing as a way to gain assurance in the security of systems by attempting to breach them using techniques similar to those used by adversaries.
Understanding the anatomy of a penetration test helps decision-makers know what they are paying for, what to expect, and how to judge whether the exercise delivers meaningful security value.
This guide breaks down each phase of a UK penetration test and explains what happens behind the scenes.
Why UK Businesses Need to Understand the Process
Cyber threats facing UK organisations have evolved rapidly. Attackers are no longer relying solely on obvious vulnerabilities. They chain together small weaknesses, exploit misconfigurations, abuse exposed APIs, and target overlooked third-party integrations.
That is why a proper penetration test focuses on real-world attack paths, not isolated technical findings.
Whether you are commissioning your first test or reviewing your annual testing programme, understanding the process helps you:
- Scope assessments effectively
- Set realistic expectations
- Distinguish genuine manual testing from automated scanning
- Ensure actionable remediation guidance
When assessing security providers, many UK organisations also look at what CREST penetration testing involves and why recognised certification frameworks can provide greater confidence in methodology, reporting standards, and tester expertise.
Phase 1: Scoping and Pre-Engagement Planning
Every credible penetration test begins long before a tester touches your infrastructure.
The planning phase defines the legal, technical, and operational boundaries of the engagement.
This includes:
- Identifying systems in scope
- Defining testing windows
- Agreeing escalation procedures
- Establishing communication channels
- Documenting rules of engagement
For UK businesses, this phase is especially critical because poorly scoped testing can cause operational disruption.
For example, testing a production payment gateway without agreed safeguards could trigger service outages.
During this stage, organisations also choose the testing approach:
Black-box testing
Testers receive minimal information, simulating an external attacker.
Grey-box testing
Limited access or credentials are provided.
White-box testing
Full architectural knowledge is shared for deeper assessment.
The right choice depends on your security goals.
Phase 2: Reconnaissance and Intelligence Gathering
Once authorisation is confirmed, testers begin reconnaissance.
This is where they gather intelligence about the target environment.
Passive reconnaissance may include:
- DNS enumeration
- Public record analysis
- Certificate transparency logs
- Metadata extraction
- Reviewing exposed repositories
Active reconnaissance may involve:
- Port scanning
- Service fingerprinting
- Application mapping
This phase often reveals surprising exposures.
A forgotten staging server, exposed admin panel, or leaked credentials in public repositories can provide an attacker with an initial foothold.
This intelligence forms the attack surface map that guides the rest of the engagement.
Phase 3: Vulnerability Discovery and Enumeration
This is where testing becomes highly technical.
Security consultants analyse identified assets to uncover weaknesses such as:
- Authentication flaws
- Misconfigurations
- Injection vulnerabilities
- Weak access controls
- Outdated software
- Privilege escalation paths
Automated tools assist here, but manual validation is what separates genuine penetration testing from commodity scanning.
A scanner may flag 200 possible issues.
An experienced tester identifies which ones are exploitable and which represent meaningful business risk.
This is also why many businesses compare penetration testing vs red teaming before commissioning an assessment, as each approach serves a different purpose depending on your organisation’s security maturity and objectives.
Phase 4: Controlled Exploitation
This is the phase many people imagine when they hear the term “ethical hacking.”
Here, testers attempt to exploit validated vulnerabilities under tightly controlled conditions.
The objective is not disruption.
The objective is proof.
A professional tester may demonstrate:
- Access to restricted systems
- Privilege escalation
- Lateral movement
- Sensitive data exposure
- Authentication bypass
For example, exploiting a vulnerable web form might lead to database access, which then exposes credentials that unlock internal administrative systems.
This chained exploitation reveals the real-world business impact of seemingly low-risk weaknesses.
That context is what boards and security leaders need.
Phase 5: Post-Exploitation Analysis
Finding access is only part of the story.
Post-exploitation answers the more important question:
What could an attacker actually do next?
This phase assesses:
- Data accessible after compromise
- Potential privilege expansion
- Lateral movement opportunities
- Persistence mechanisms
- Business-critical system exposure
This is often where organisations discover the true severity of their security gaps.
A medium-risk flaw may become critical when combined with weak segmentation or excessive privileges.
Phase 6: Reporting and Risk Prioritisation
The final deliverable should never be a generic vulnerability dump.
A quality UK penetration testing report includes:
- Executive summary
- Technical findings
- Severity ratings
- Evidence of exploitation
- Business impact analysis
- Practical remediation steps
The best reports prioritise findings based on exploitability and operational impact.
Many UK organisations use these reports to support cyber insurance requirements, client due diligence, and internal governance reviews.
For organisations building a long-term security strategy, understanding how often penetration testing should be carried out in the UK is just as important as knowing how the process works. Testing frequency depends on infrastructure changes, compliance obligations, and overall risk exposure.
Phase 7: Remediation Validation
A penetration test is incomplete without follow-up validation.
Once fixes are implemented, testers retest affected systems to confirm vulnerabilities have been resolved.
This ensures remediation efforts genuinely reduce risk rather than simply shifting the problem elsewhere.
The strongest UK security programmes treat penetration testing as a continuous improvement cycle rather than a one-off annual exercise.
What Makes a Good UK Penetration Test?
A high-quality engagement should provide:
Clarity
Clear scope and objectives
Depth
Manual validation beyond automated scanning
Realism
Attack simulation aligned to current threats
Actionability
Practical remediation guidance
Assurance
Evidence your security controls work
If the output is little more than exported scanner results, your organisation has not received a true penetration test.
FAQs
What is the average duration of a penetration test in the UK?
The duration depends on the scope, complexity, and size of the environment being assessed. A standard web application test may take 5–7 days, while larger enterprise infrastructure assessments can extend to several weeks.
Is penetration testing mandatory for UK businesses?
Penetration testing is not legally mandatory for every UK business, but it is often required for organisations handling payment data, operating in regulated sectors, or meeting contractual security obligations from clients, partners, or insurers.
What is the difference between vulnerability scanning and penetration testing?
Vulnerability scanning uses automated tools to identify potential weaknesses, whereas penetration testing involves manual validation by security professionals who attempt controlled exploitation to confirm risks and demonstrate their actual business impact.
Should SMEs invest in penetration testing?
Yes. Small and medium-sized businesses are increasingly targeted because attackers often assume weaker defences. Regular penetration testing helps SMEs identify exploitable weaknesses early, strengthen security controls, and build trust with customers.
How often should penetration testing be performed?
Most UK organisations should conduct penetration testing at least once annually. Additional testing should be performed after significant infrastructure upgrades, new application deployments, cloud migrations, or any major changes that could introduce security risks.
Does CREST certification matter?
Yes, particularly for UK organisations seeking recognised assurance standards. CREST-certified providers follow strict methodologies and demonstrate technical competence, giving businesses greater confidence in the quality, reliability, and credibility of the penetration testing results.
